Member-only story
Crimson — AppSec firearm I
Setting up the environment for testing and crimson_recon explanation.

INTRODUCTION
It has been a couple of months since the last article about the automatization of Web Application Penetration Testing. From that moment, Crimson had grown up from those few code snippets described in previous articles, and if you are a kind of code-archeologist, you can check them here:
- Automation of the reconnaissance phase during Web Application Penetration Testing I
- Automation of the reconnaissance phase during Web Application Penetration Testing II
- Automation of the reconnaissance phase during Web Application Penetration Testing III
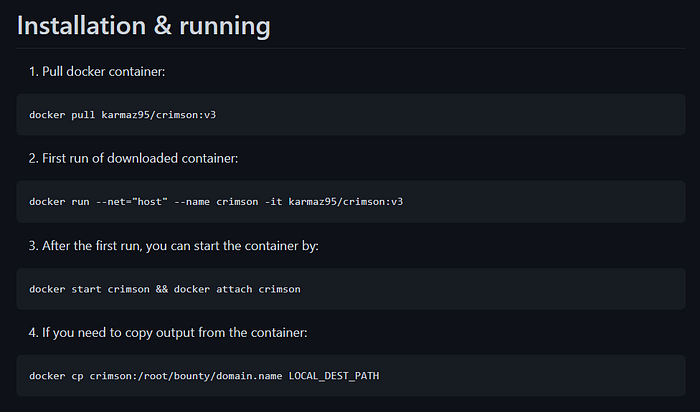
The whole repository is much bigger now, and the tool is now a Docker container you can run on Windows and *nix-based systems.
In the following articles, I will guide you through the Web Application Penetration Testing process using Crimson and Burp Suite Pro on the randomly chosen Bug Bounty program with *.domain.tld as scope.
I won’t describe every part of the Crimson code — if you are curious how everything works you can check it by yourself in the Github repository.
ENVIRONMENT SETUP
I will be using Kali Linux open-source penetration testing distribution natively, from Windows 11 using WSL2 with Docker Crimson container.

- Burp Suite Professional could be installed from this link.
- To install WSL2 on Windows 11, open Windows PowerShell as an Administrator and type
wsl --install. - Install Kali Linux using
wsl --install -d kali-linuxin the same Windows PowerShell terminal or visit the Microsoft Store. - You can download and install Docker software from this link.